As we continue our series on exploring the use of Gemini 3 to produce brief "backgrounder" reports to provide context to important topics in the news, here is Gemini 3.1 Pro's look at counterterrorism trends in India and the use of crypto to finance terrorism around the globe.
Write a deeply researched 5-6 page "backgrounder" report on the topic below for a foreign policy researcher analyst that provides sufficient background, history, context and information such that someone without any previous knowledge of this topic would have enough background context to fully understand it. TOPIC: Counterterrorism in India in recent decades through present. Discuss both major terrorism events and smaller significant ones, trends, patterns and the response of the state and how it is approaching counterterrorism.
TO: Foreign Policy Research Analyst
FROM: Strategic Intelligence Desk
DATE: April 25, 2026
SUBJECT: Backgrounder: Counterterrorism in India – Historical Context, Recent Trends (Through Early 2026), and State Response
EXECUTIVE SUMMARY
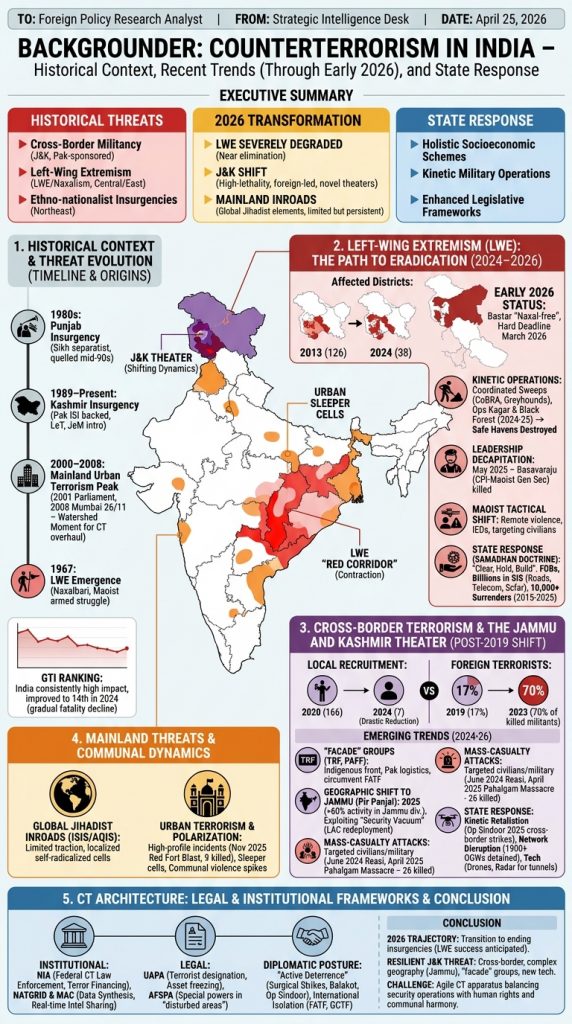
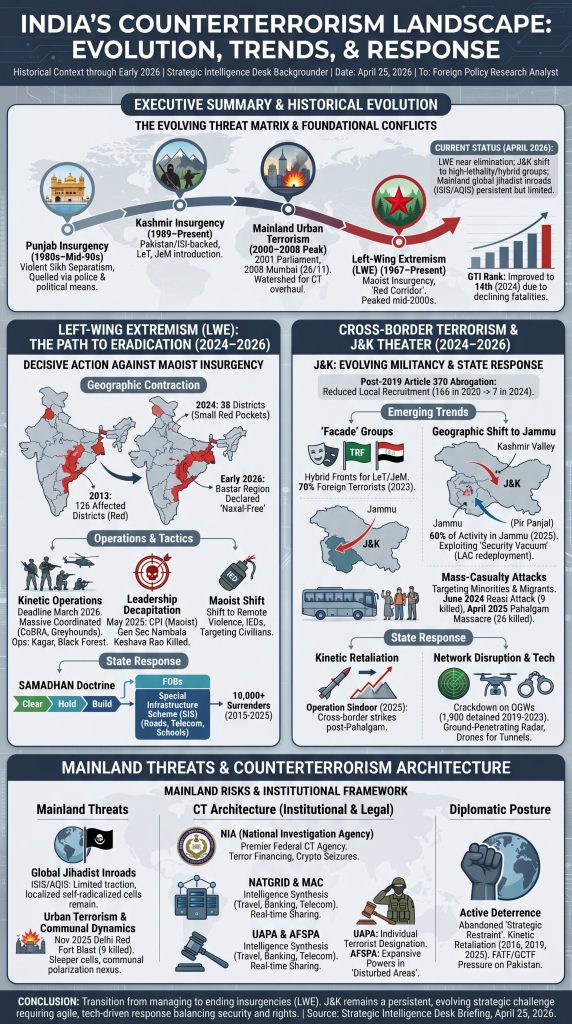
For decades, India has faced a complex internal security environment characterized by a multi-front terrorism threat. Historically, this has been defined by three primary vectors: cross-border militancy in Jammu and Kashmir (J&K) sponsored by neighboring Pakistan, a decades-long communist insurgency known as Left-Wing Extremism (LWE) or Naxalism in central/eastern India, and ethno-nationalist insurgencies in the Northeast.
As of April 2026, India’s counterterrorism (CT) landscape has undergone a profound transformation. State responses—ranging from holistic socioeconomic development schemes to kinetic military operations and enhanced legislative frameworks—have severely degraded the LWE threat, putting it on the verge of complete elimination[1][2]. Conversely, while overall terror incidents in J&K have declined, the region has seen a dangerous shift toward high-lethality, mass-casualty attacks led by foreign terrorists and "hybrid" militant groups operating in geographically novel theaters[3][4]. Concurrently, global jihadist elements (ISIS/Al-Qaeda) have made limited but persistent inroads into the mainland, requiring robust financial and digital countermeasures[5].
This backgrounder provides a comprehensive overview of India's CT landscape, focusing on recent developments up to early 2026, the evolution of terror tactics, and the overarching strategy of the Indian security apparatus.
1. HISTORICAL CONTEXT & THE EVOLUTION OF THE THREAT
India’s modern counterterrorism apparatus was forged in the crucible of several overlapping conflicts:
- The Punjab Insurgency (1980s): A violent Sikh separatist movement that was largely quelled by the mid-1990s through a mix of heavy-handed police operations and political accommodation.
- The Kashmir Insurgency (1989–Present): A separatist movement heavily backed by Pakistan’s Inter-Services Intelligence (ISI), introducing groups like Lashkar-e-Taiba (LeT) and Jaish-e-Mohammed (JeM) to the region[4][6].
- Mainland Urban Terrorism: Peaked between 2000 and 2008, culminating in the 2001 Parliament attack and the devastating 2008 Mumbai attacks (26/11) carried out by LeT[5][6]. The Mumbai attacks exposed severe intelligence and coordination failures, serving as a watershed moment that forced a complete overhaul of India's CT architecture.
- Left-Wing Extremism (LWE): Emerging in 1967 in Naxalbari, West Bengal, the Maoist insurgency sought to overthrow the state through armed struggle, exploiting the grievances of marginalized tribal populations[7]. By 2006, the Indian government labeled LWE as the "single biggest internal security threat"[5].
According to the Global Terrorism Index (GTI), India has consistently ranked among the countries most impacted by terrorism, though its position improved to 14th in the 2024 rankings due to a gradual decline in overall fatalities over the previous decade[8].
2. LEFT-WING EXTREMISM (LWE): THE PATH TO ERADICATION (2024–2026)
The Maoist insurgency, operating across a "Red Corridor" spanning states like Chhattisgarh, Jharkhand, and Odisha, has experienced a precipitous decline.
Recent Trends and Operations:
- Geographic Contraction: The number of LWE-affected districts plummeted from 126 in 2013 to just 38 in 2024[2][9]. By early 2026, the Union Home Ministry declared the historically impenetrable Bastar region of Chhattisgarh effectively "Naxal-free"[10].
- Decisive Kinetic Operations: The government established a hard deadline of March 2026 to eliminate LWE[1][2]. To achieve this, security forces launched massive coordinated sweeps involving central paramilitary and specialized state police (e.g., CoBRA, Greyhounds)[10]. Operations like Kagar (2024-2025) and Black Forest (April–May 2025) resulted in the destruction of safe havens[1][7][9].
- Leadership Decapitation: A major turning point occurred in May 2025, when Nambala Keshava Rao (Basavaraju), the General Secretary of the CPI (Maoist), was killed alongside over two dozen cadres[7][9].
- Maoist Tactical Shift: Weakened and outgunned, Maoist rebels have largely abandoned direct engagements, shifting toward the use of remote violence and Improvised Explosive Devices (IEDs), while targeting civilians accused of being police informants[1].
The State Response (SAMADHAN Doctrine):
India shifted from a purely military response to a "Clear, Hold, Build" counter-insurgency doctrine codified in the 2015 National Policy and Action Plan[7][10]. The operational blueprint, the SAMADHAN doctrine (launched in 2017), synchronizes intelligence-led offensives with aggressive development[7][10]. As regions are "cleared," the government establishes Forward Operating Bases (FOBs) and funnels billions of rupees into the Special Infrastructure Scheme (SIS) to build roads, telecom towers, and schools, integrating formerly alienated tribal populations[2][10]. Between 2015 and 2025, over 10,000 Naxalites surrendered under state rehabilitation policies[9].
3. CROSS-BORDER TERRORISM & THE JAMMU AND KASHMIR THEATER
The security landscape in J&K shifted dramatically following the August 2019 abrogation of Article 370, which revoked the region's special autonomous status[3][11]. While New Delhi implemented heavy security crackdowns and development initiatives that drastically reduced local recruitment into terror groups (dropping from 166 youths in 2020 to just 7 in 2024), the character of the militancy evolved in lethal ways[11].
Emerging Trends (2024–2026):
- The Rise of "Facade" Groups: To circumvent international scrutiny and the Financial Action Task Force (FATF), Pakistan-based legacy groups like LeT and JeM spawned "hybrid" front organizations[3]. Groups such as The Resistance Front (TRF) and the People’s Anti-Fascist Front (PAFF) project an indigenous, secular-resistance façade while relying heavily on Pakistani logistics and foreign terrorists (FTs)[3][5][11]. By 2023, nearly 70% of militants killed in J&K were foreign nationals, a sharp increase from 17% in 2019[11].
- Geographic Shift to Jammu: With the Kashmir Valley highly militarized, militancy strategically relocated southward into the Hindu-majority Jammu division—specifically the rugged, forested Pir Panjal range (Rajouri, Poonch, Doda)[3][4][11]. In 2025, over 60% of all violent militant activity in J&K occurred in the Jammu division (up from 5% in 2018)[4]. Militants exploited a "security vacuum" created when India redeployed thousands of troops from this region to the Line of Actual Control (LAC) following the 2020 border standoff with China[4][12].
- Mass-Casualty and Targeted Attacks: Terrorists increasingly targeted military convoys and minority civilians (Hindus and non-local migrant workers) to incite communal tensions and grab headlines[4][11]. Significant events include the June 2024 Reasi bus attack (9 pilgrims killed) and the devastating April 22, 2025 Pahalgam Massacre, where TRF/LeT militants executed 26 unarmed Hindu tourists[3][4][6][12].
The State Response:
India's response to J&K militancy has become increasingly coercive and tech-driven.
- Kinetic Retaliation: The 2025 Pahalgam massacre triggered Operation Sindoor, a limited military offensive targeting militant bases across the border in Pakistan-administered Kashmir, leading to intense bilateral cross-border shelling[3][4].
- Network Disruption: Agencies launched massive crackdowns on Over Ground Workers (OGWs)—the logistical backbone of terror groups. Between 2019 and 2023, over 1,900 OGWs were detained[3]. Forces are increasingly utilizing ground-penetrating radar, seismic sensors, and drones to uncover cross-border infiltration tunnels[13].
4. MAINLAND THREATS, RADICALIZATION, AND COMMUNAL DYNAMICS
While J&K and LWE dominate the kinetic landscape, internal security agencies continuously monitor threats in the broader Indian mainland.
- Global Jihadist Inroads: Groups like ISIS and Al-Qaeda in the Indian Subcontinent (AQIS) have struggled to gain mainstream traction among India's 180 million Muslims, though highly localized, self-radicalized cells remain a concern[5].
- Urban Terrorism & Communal Polarization: The intersection of terrorism and domestic communal polarization remains a flashpoint. High-profile, isolated incidents—such as a deadly car explosion near Delhi's Red Fort on November 10, 2025 (which killed 9 people)—have raised alarms about sleeper cells operating in major metropolises[5][14]. Terror incidents are occasionally followed by spikes in communal violence, complicating the law enforcement response[14].
5. THE COUNTERTERRORISM ARCHITECTURE: LEGAL AND INSTITUTIONAL FRAMEWORKS
India has progressively tightened its CT infrastructure to emphasize pre-emption, intelligence synthesis, and financial asphyxiation.
Institutional Machinery:
- National Investigation Agency (NIA): Formed post-2008, the NIA acts as India's premier federal counterterrorism law enforcement agency. It has aggressively pursued terror financing, seizing assets linked to hawala networks and cryptocurrency[13].
- NATGRID & MAC: The National Intelligence Grid (NATGRID) and the Multi-Agency Centre (MAC) serve to synthesize massive data pools (travel, banking, telecommunications) and share real-time intelligence among federal and state agencies, eliminating the silos that enabled the 26/11 attacks[13].
Legal Frameworks:
- UAPA (Unlawful Activities Prevention Act): The primary anti-terror legislation. Recent amendments allow the state to designate individuals (not just organizations) as terrorists, enabling the freezing of assets[5][14].
- AFSPA (Armed Forces Special Powers Act): Applied in "disturbed areas" (like parts of J&K and the Northeast), AFSPA grants security forces expansive operational powers and immunity from civilian prosecution. While military leaders argue it is essential for asymmetric warfare, human rights organizations frequently criticize the act[5].
Diplomatic and Strategic Posture:
India has abandoned the doctrine of "strategic restraint" in favor of "active deterrence." Beginning with the 2016 surgical strikes, the 2019 Balakot airstrikes, and the 2025 Operation Sindoor cross-border strikes, New Delhi has normalized kinetic military retaliation against state sponsors of terrorism[3][6]. Diplomatically, India has heavily leveraged international forums like the FATF and the Global Counterterrorism Forum (GCTF) to isolate Pakistan financially and politically[5][6].
CONCLUSION
As of 2026, India's counterterrorism trajectory reflects a transition from managing insurgencies to decisively ending them, as seen in the anticipated eradication of Left-Wing Extremism[2][7]. However, the resilient nature of cross-border terrorism in Jammu and Kashmir underscores a persistent strategic challenge[6]. The shift of militant operations into complex geographies like Jammu, the utilization of proxy "facade" groups, and the integration of new technologies (drones, encrypted communications, crypto-financing) dictate that India’s CT apparatus must remain agile[3][12][13]. Balancing aggressive intelligence-led security operations with the preservation of human rights and communal harmony remains the defining challenge for India's internal security strategy moving forward[6][14].
Sources
Create a large illustrated explainer poster designed to be printed on a large-format poster printer and hung up on the wall that narrates the attached briefing as a single large poster that can be printed and hung on a wall that outlines all of the core details. It should cover all of its key details and be in portrait orientation.
And in 4K, which helps Nano Banana Pro's rendering abilities:
Now, let's repeat for the role of crypto in terrorism financing:
Write a deeply researched 5-6 page "backgrounder" report on the topic below for a foreign policy researcher analyst that provides sufficient background, history, context and information such that someone without any previous knowledge of this topic would have enough background context to fully understand it. TOPIC: The role of crypto in financing and supporting terrorism around the world. Give specific examples, making sure to include examples from each part of the world and examples of different ways crypto is being used in terrorism financing.
TO: Foreign Policy Research Analyst
FROM: Director of Threat Finance Intelligence
DATE: April 25, 2026
SUBJECT: BACKGROUNDER: The Role of Cryptocurrency in Financing and Supporting Global Terrorism
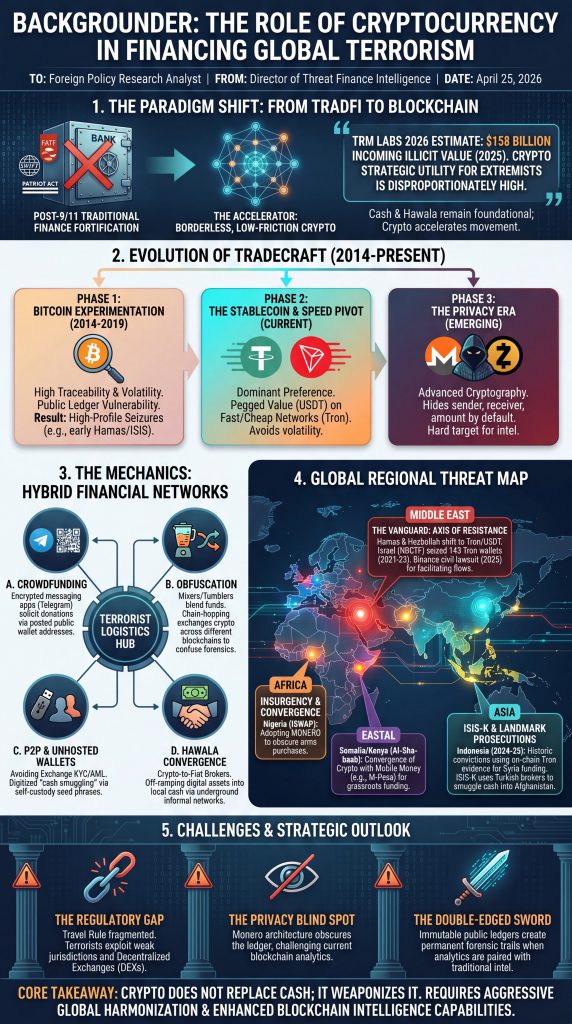
EXECUTIVE SUMMARY
Over the past decade, the global counter-terrorism community has witnessed a paradigm shift in illicit finance. Following the post-9/11 fortification of the traditional banking system, terrorist organizations increasingly migrated to alternative remittance systems. Today, that migration has extended to the blockchain. While cash and informal value transfer systems (like hawala) remain foundational to terrorist logistics, cryptocurrency has emerged as a borderless, low-friction accelerator for raising, moving, and storing illicit funds[1][2].
According to blockchain intelligence firm TRM Labs’ 2026 Crypto Crime Report, illicit cryptocurrency wallets received an estimated $158 billion in incoming value in 2025[3]. While only a fraction of this is directly tied to terrorism, the strategic utility of digital assets for extremist groups is disproportionately high[1][3]. Terrorist networks have rapidly evolved from experimenting with highly traceable Bitcoin to utilizing fast, low-fee networks (like Tron), stablecoins pegged to the US dollar (like Tether/USDT), and anonymity-enhanced privacy coins (like Monero)[4][5].
This backgrounder provides a comprehensive overview of the history, mechanics, and regional typologies of cryptocurrency-based terrorist financing. It is designed to equip policymakers and foreign policy analysts with the foundational context required to understand how digital assets are weaponized by extremist groups across the Middle East, Africa, Asia, the Americas, and Europe.
1. BACKGROUND AND EVOLUTION: FROM AL-QAEDA TO WEB3
To understand the nexus between cryptocurrency and terrorism, one must understand the regulatory environment of the traditional financial (TradFi) sector. Following the September 11, 2001 attacks, the U.S. and its allies weaponized the global banking system. Through the Patriot Act, the SWIFT banking network, and the Financial Action Task Force (FATF), Washington effectively walled off the global financial system from designated terrorist entities.
For nearly two decades, terrorist groups relied heavily on cash smuggling, illicit trade, and hawaladars (informal brokers). However, the introduction of Bitcoin in 2009 offered a new theoretical avenue: a decentralized, peer-to-peer digital currency outside the control of any central bank or government[6].
The Evolution of the Threat:
- Phase 1: Bitcoin Experimentation (2014–2019): Early adoption was rudimentary. Groups like the military wing of Hamas (the Izz al-Din al-Qassam Brigades) and early ISIS affiliates began posting Bitcoin wallet addresses on social media to solicit donations[7][8]. However, Bitcoin relies on a public, immutable ledger. Blockchain intelligence firms (such as Chainalysis and TRM Labs) easily traced these funds, leading to high-profile seizures by the U.S. Department of Justice[2][8].
- Phase 2: Stablecoins and Fast Networks (2020–Present): Recognizing Bitcoin’s traceability and price volatility, terrorists pivoted. By 2023–2026, the overwhelming preference for terror financing shifted to Tether (USDT)—a stablecoin pegged 1:1 to the US dollar—transferred over the Tron network[4]. Tron is favored because it is faster and cheaper than the Bitcoin or Ethereum networks, and USDT protects illicit actors from the extreme price volatility of traditional cryptocurrencies[4][6].
- Phase 3: The Privacy Era: Sophisticated networks, particularly in Africa and among Western domestic extremists, are increasingly adopting "privacy coins" like Monero (XMR) and Zcash (ZEC), which use advanced cryptography to hide transaction amounts, senders, and receivers by default[5][9].
2. THE MECHANICS: HOW TERRORISTS EXPLOIT CRYPTO
Terrorist organizations do not use cryptocurrency in a vacuum; they integrate it into broader hybrid financial networks. The primary typologies of use include:
A. Crowdfunding and Social Media Solicitations
Terrorist groups leverage encrypted messaging apps like Telegram to run crowdfunding campaigns. For example, during the lead-up to the October 2023 attacks, Hamas-aligned entities like "Gaza Now" explicitly posted wallet addresses for Tether and Tron on their Telegram channels[10].
B. Obfuscation Techniques (Mixers, Tumblers, and Chain-Hopping)
To break the trail of funds, terrorists use "mixers" (services that blend potentially identifiable cryptocurrency with large amounts of other funds to obscure the trail back to the fund's original source)[11]. They also employ "chain-hopping"—rapidly exchanging one cryptocurrency (e.g., Bitcoin) for another (e.g., Monero) across decentralized exchanges to confuse blockchain investigators[11].
C. Peer-to-Peer (P2P) Exchanges and Unhosted Wallets
To avoid the Know-Your-Customer (KYC) and Anti-Money Laundering (AML) checks required by major exchanges like Coinbase or Binance, terror financiers use P2P platforms or "unhosted" (self-custodial) wallets[5][12]. This allows them to transfer millions of dollars instantly via a USB drive or a piece of paper containing a seed phrase, effectively digitizing the act of cash smuggling.
D. Convergence with Hawala and Brokers
In regions with low banking penetration, crypto is converted into local fiat currency through underground brokers[1][12]. A financier might send USDT to an informal exchange in Turkey or Dubai, where a broker takes a commission and hands physical cash to an operative in Syria or Afghanistan[13].
3. REGIONAL CASE STUDIES
The strategic application of cryptocurrency varies wildly depending on a region's digital infrastructure, the nature of the extremist group, and local regulatory enforcement.
The Middle East: The Vanguard of Crypto-Terror
The Middle East serves as the most mature ecosystem for crypto-terrorism, heavily utilized by Iran’s "Axis of Resistance" (Hamas, Hezbollah, and Palestinian Islamic Jihad)[4].
- Hamas and the Shift to Tron: Prior to the October 2023 attacks, Hamas raised tens of millions in cryptocurrency[4]. Due to the transparency of Bitcoin, Hamas explicitly announced in 2023 it would no longer use it for donations[7]. Instead, they migrated to the Tron network. Between 2021 and late 2023, Israel’s National Bureau for Counter Terror Financing (NBCTF) seized 143 Tron wallets linked to Hamas, Hezbollah, and the PIJ[4].
- Hezbollah and State Proxies: The US Treasury and Israeli authorities have traced millions of dollars flowing to Hezbollah and Iran's Islamic Revolutionary Guard Corps (IRGC) via digital assets[10][14]. These groups blend crypto with traditional money laundering, utilizing Gaza-based brokers like Buy Cash Money and Money Transfer Company to interface with global exchanges like Binance[1]. In late 2025, victims of the October 7 attacks filed a massive civil lawsuit against Binance for allegedly facilitating these exact terror financing networks[1].
Africa: Insurgency, Privacy Coins, and Mobile Money Convergence
In Sub-Saharan Africa, where traditional banking infrastructure is often lacking, crypto has become a vital lifeline for Islamic State affiliates and regional insurgents[3][12].
- Nigeria (Boko Haram & ISWAP): The Islamic State West Africa Province (ISWAP) has demonstrated remarkable financial adaptability. As military crackdowns disrupted their traditional extortion and kidnapping revenues, ISWAP media channels began soliciting funds in Monero[5]. Because Monero obscures transaction data, it allows ISWAP to purchase weapons and drones across porous African borders without detection by state intelligence[3][5]. Nigeria’s status as a global leader in grassroots crypto adoption provides a vast ocean of transactions in which terrorists can hide[12][15].
- South Africa and Somalia (Al-Shabaab): South Africa has emerged as a financial hub where ISIS sympathizers funnel proceeds from ransom kidnappings through crypto channels to al-Shabaab in Somalia and ISIS cells globally[15]. In Kenya, there is an emerging, highly concerning convergence between digital crypto wallets and ubiquitous mobile money platforms (like M-Pesa), allowing groups like Al-Shabaab to seamlessly move funds from the blockchain directly into the pockets of grassroots operatives[12].
Asia: ISIS-K and Landmark Prosecutions
In South and Southeast Asia, tech-savvy terrorist cells are utilizing stablecoins for cross-border logistics, prompting a swift response from regional intelligence agencies[8][11].
- Indonesia: Indonesia has become a critical battleground for crypto-terrorism enforcement. In 2024 and 2025, Indonesian counter-terrorism unit Densus 88 and the financial intelligence unit (PPATK) secured three landmark terrorism convictions relying almost entirely on blockchain forensics[16][17]. The defendants were convicted of utilizing the Tron network to send over 49,000 USDT to ISIS-affiliated fundraising campaigns in Syria[16][17]. This marked a historic moment where on-chain evidence was used as the primary anchor in a non-Western national court[17].
- Afghanistan/Pakistan (ISIS-K): The Islamic State Khorasan Province (ISIS-K) leverages Tether and Tron to fund its operations and bypass the heavily sanctioned Taliban-run financial system[8]. Funds are often routed through virtual asset exchanges in Turkey, where they are cashed out and smuggled into Afghanistan via hawala networks[13].
The Americas and Europe: Domestic Extremism and Narco-Terrorism
In the West, cryptocurrency is heavily utilized by Domestic Violent Extremists (DVEs), far-right groups, and Latin American cartels engaging in narco-terrorism[9].
- White Supremacy and the Radical Right (US & Europe): Following the 2017 Charlottesville rally, major financial processors (PayPal, Visa, GoFundMe) systematically de-platformed neo-Nazi and white supremacist groups[18]. In response, these groups heavily adopted Bitcoin and privacy coins[9][19]. Far-right platforms and extremist militias utilize crypto to crowdfund, publish decentralized manifestos, and purchase weapons[9]. The anonymity of crypto aligns seamlessly with the anti-government, anti-central-bank ideology of many domestic extremist groups[20].
- Latin America: In the Andean region, the remnants of insurgent groups (like the FARC and ELN in Colombia) and violent cartels are utilizing Peer-to-Peer (P2P) crypto exchanges to launder proceeds from drug trafficking and illegal mining[9][21]. Furthermore, South American security agencies in 2025 noted the overlapping use of Monero by radical environmental organizations and anti-globalist militias[9]. Cartels in this region increasingly intersect with Chinese-Language Money Laundering Networks (CMLNs) operating via Telegram, creating a sophisticated underground economy[22].
4. CHALLENGES IN COUNTERING THE THREAT
Combating cryptocurrency-based terrorism financing presents unique challenges for the foreign policy and national security establishment:
- The "Travel Rule" Compliance Gap: The FATF has mandated the "Travel Rule" for crypto, requiring exchanges to share sender/receiver data for transactions above a certain threshold. However, global implementation is heavily fragmented. Terrorists exploit regulatory arbitrage, routing funds through jurisdictions with weak AML laws or using decentralized exchanges (DEXs) that require no ID[8][12].
- The Threat of Privacy Coins: While platforms like TRM Labs and Chainalysis can successfully de-anonymize transactions on public blockchains like Bitcoin and Tron[2], privacy coins like Monero represent a critical blind spot for intelligence agencies, as the cryptographic architecture obscures the ledger[5][9].
- The Dual-Use Nature of Technology: The very tools designed to protect human rights activists and dissidents in authoritarian regimes (unhosted wallets, decentralized finance, encrypted messaging) are the exact same tools utilized by Hamas and ISIS[5][6].
5. CONCLUSION AND STRATEGIC OUTLOOK
Cryptocurrency has permanently altered the landscape of terrorist financing. It has flattened geography, allowing an ISIS sympathizer in Indonesia to fund a militant in Syria instantly, or a white supremacist in Europe to finance a domestic terror cell in the United States without passing through a single traditional bank[9][16].
However, the blockchain is a double-edged sword. Unlike physical cash, public blockchains are permanent and immutable[15]. As demonstrated by the recent convictions in Indonesia and Israeli wallet seizures, when law enforcement pairs advanced blockchain analytics with traditional intelligence, cryptocurrency leaves an indelible forensic trail[4][17].
For the foreign policy analyst, the core takeaway is that crypto does not replace cash; it weaponizes it[5]. Future counter-terrorism strategies cannot treat cryptocurrency as a niche tech issue. It must be addressed holistically through aggressive international regulatory harmonization, the sanctioning of non-compliant digital asset platforms, and the expansion of real-time blockchain intelligence capabilities across global allied intelligence services.
Sources
- nominis.io
- chainalysis.com
- trmlabs.com
- jpost.com
- nominis.io
- binance.com
- gigazine.net
- gnet-research.org
- tacticsinstitute.com
- house.gov
- worldscientific.com
- researchgate.net
- westpoint.edu
- unav.edu
- adf-magazine.com
- trmlabs.com
- binance.com
- researchgate.net
- counterextremism.com
- ccn.com
- secretariat-intl.com
- chainalysis.com
And let's ask for a 4K infographic of it:
Create a large illustrated explainer poster designed to be printed on a large-format poster printer and hung up on the wall that narrates the attached briefing as a single large poster that can be printed and hung on a wall that outlines all of the core details. It should cover all of its key details and be in portrait orientation.